Substantiate security claims before buyers scrutinise them.
SOC 2, uptime, detection rate, and benchmark claims are the statements enterprise buyers test hardest. Veridat connects each claim to its certification, test result, or benchmark report : and keeps that link current.
Why security claims are the highest-scrutiny category.
ASA CAP Code rule 3.7 requires documentary evidence to be held before objective claims : including performance and security claims : are published. For cybersecurity vendors, claims like 'industry-leading detection rates' or '99.99% uptime' are objective performance statements that require substantiated proof held at the time of publication.
Enterprise buyers conduct increasingly rigorous vendor due diligence. A claim that cannot be evidenced during a procurement process is a deal risk. Veridat gives your sales team access to approved, evidence-backed claims : not unsubstantiated marketing language.
“ASA CAP Code rule 3.7: 'Marketers must hold documentary evidence to prove all claims that are capable of objective substantiation.'”
How Veridat helps
- Evidence held before the claim is published : not retrieved after a complaint
- Timestamped approval records with named approver and conditions
- Lifecycle alerts when evidence expires or conditions change
The claims cybersecurity teams need to govern.
Each of these claim types requires documentary evidence to be held before publication. Veridat governs the intake, evidence, and approval of each one.
Certification claims
'SOC 2 Type II certified'
OBJECTIVEPerformance claims
'99.99% uptime across enterprise deployments'
OBJECTIVEDetection claims
'Industry-leading threat detection rates'
COMPARATIVECompliance claims
'GDPR-compliant data handling'
OBJECTIVE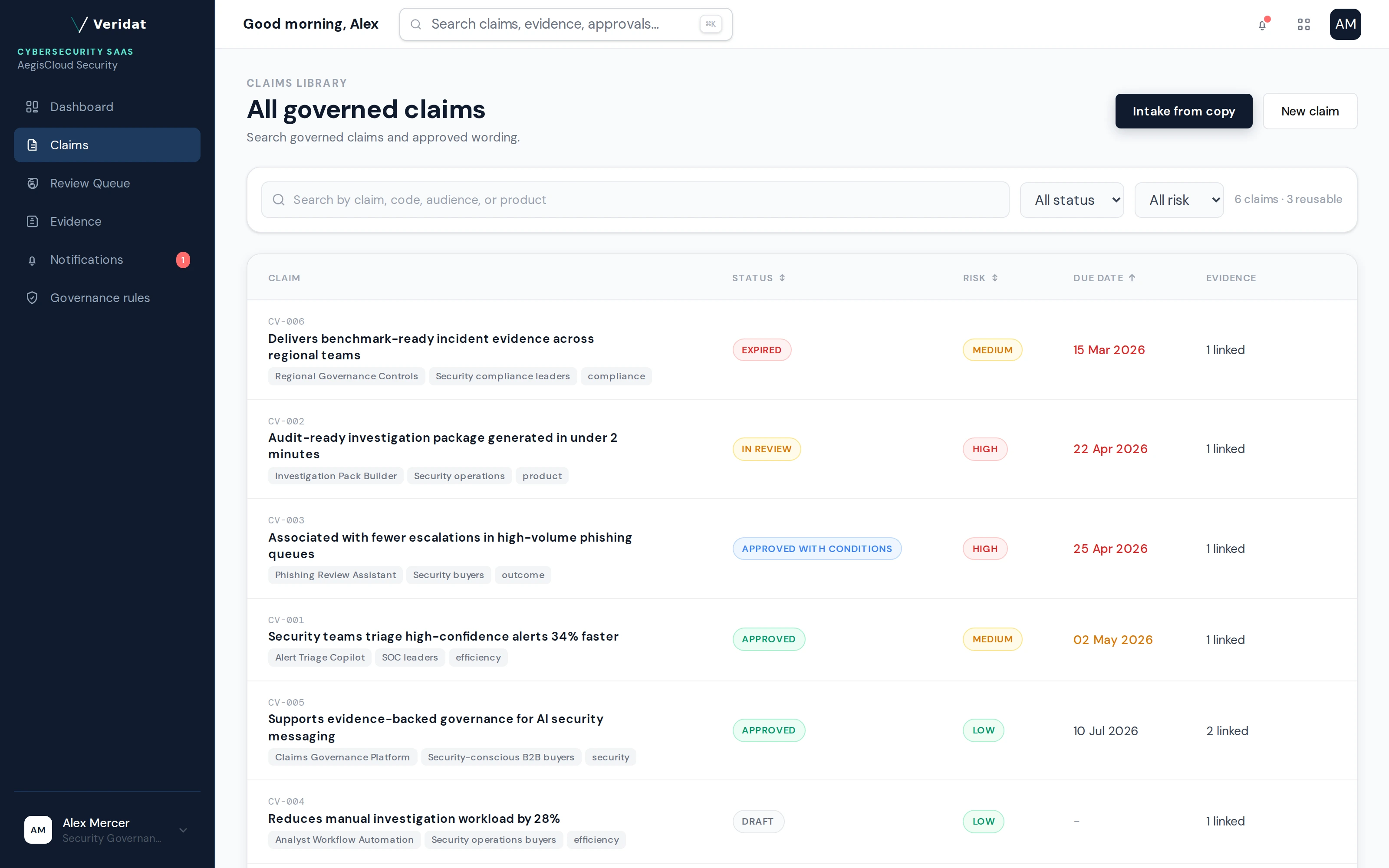
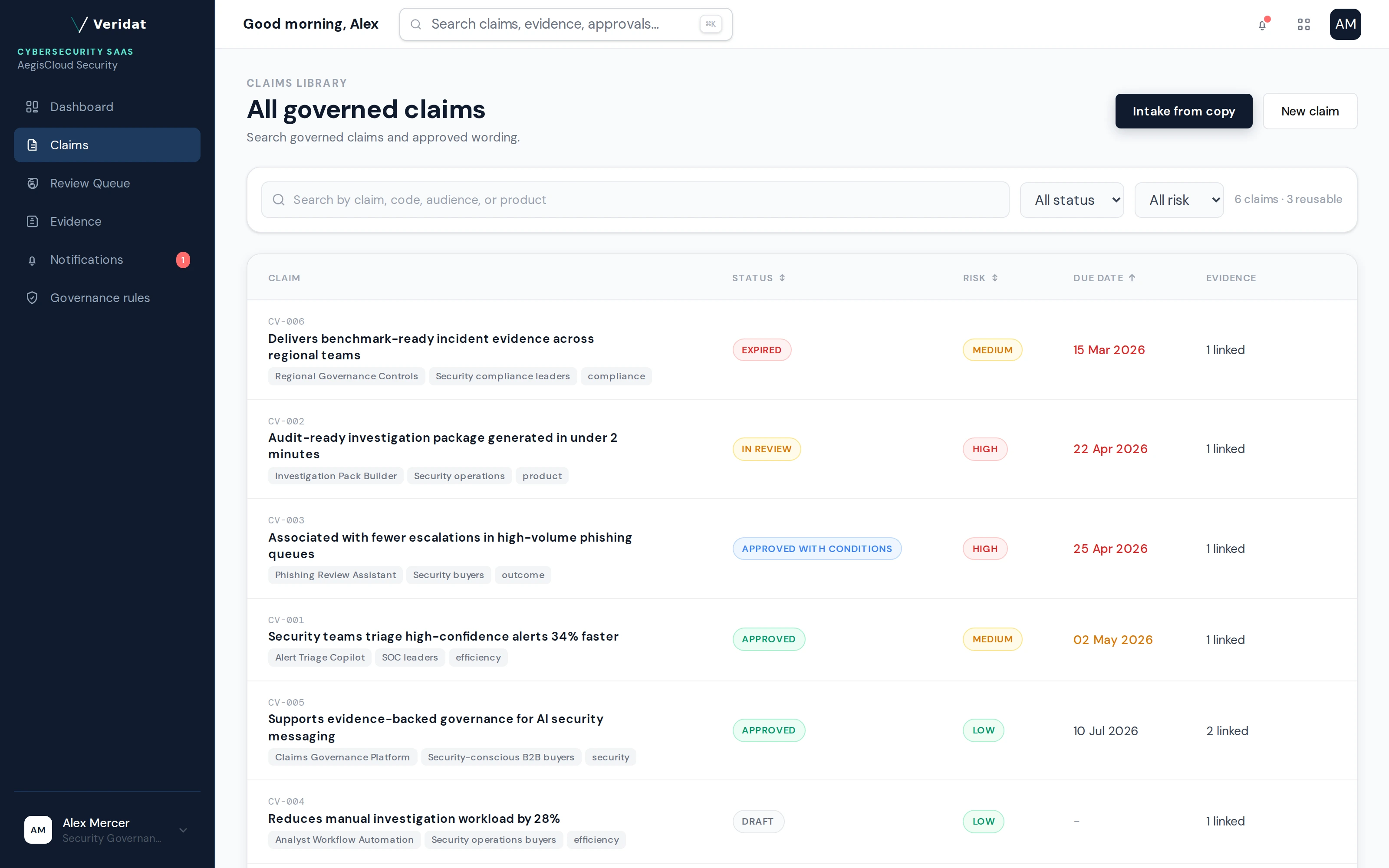
The cybersecurity claims library : every claim with its evidence, approval status, and reuse record.
How Cybersecurity teams use Veridat
Extract and classify
Paste cybersecurity copy. Veridat identifies likely claims and surfaces regulatory risk signals before review.
Attach evidence and review
Link certifications, studies, or compliance documents. Route to legal with evidence and AI signals already attached.
Approve and reuse
Approved wording : with its conditions : lives in the governed library. Reuse without a new review.
Give your sales team evidence-backed claims.
Built for teams navigating ASA CAP Code, FCA, and enterprise procurement security reviews.
14-day free trial · No credit card required · Built for UK-regulated teams